Two months on from its well published discovery and many servers are still at risk from the DROWN Vulnerability!
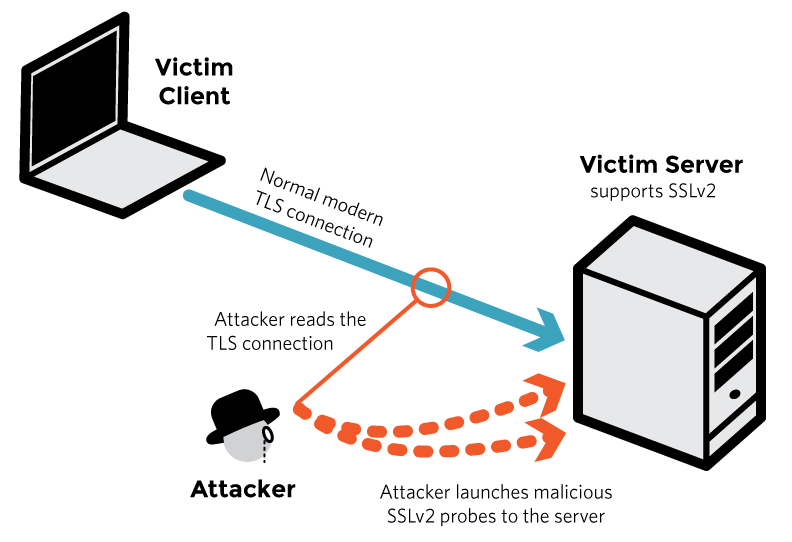
The Drown attack is a serious vulnerability which allows hackers to break encryption and read or steal sensitive communications, including passwords, credit card numbers, trade secrets, or financial data. It effects secure (HTTPS) servers and other services that rely on SSL, some of the essential protocols for Internet security. Most terrifying of all, it is estimated that 33% of secure servers are vulnerable!
Does it effect me?
This exploit effects sites that accept connections using SSL v2;
We don’t have any websites….so we’re ok….
This is a common mistake. Have you ever wondered how your emails get to your Iphone or other mobile device from you in-house Exchange server. They transit over an SSL website and unless your IT provider has updated and patched your server… you could be at risk.
How can I check?
There are many tools available for checking: Test.DROWNAttack.com runs a simple check.
Qualys also provide a more detailed analysis of many known vulnerabilities.
Visit the sites, pop in your website address and submit for a quick check.
I don’t know my website address…..
If you have an Iphone or Ipad which receives work emails your website address can be found by clicking on “Settings”, “Mail, Contacts, Calenders”, Select your Exchange account, selecting “Account” and the “Server” field is the address you’ll need to check.
It’s more common than you think. We’re finding many IT providers are not proactive in protecting their clients and this is putting their data at risk.
FibreFly offer proactive IT support and can secure your site. Don’t loose your data, or put up with poor IT support. Call us today – 01183 840 015
If this post was helpful, please re-post using the links below.



Recent Comments